[ad_1]
If you happen to’ve ever been to Cisco Dwell and seen the sales space with a show so that you can choose locks, then you realize in regards to the Cisco Superior Safety Initiatives Group (ASIG). We’re chartered with safety testing and moral hacking for all Cisco services, whether or not within the cloud or on-premises. Something Cisco sells, we have now a go at it and attempt to break it—discovering vulnerabilities as early as doable—earlier than it’s deployed on the web and reaches buyer environments.
Our Product Safety Incident Response Group (PSIRT) distributes details about found vulnerabilities to assist harden Cisco choices. You probably have a weak situation, studying learn how to exploit these vulnerabilities in a community may enable you to decide what mitigations to use and strengthen your safety posture.
Changing into a Hacker
Yearly, we have now a category referred to as Changing into a Hacker, which teaches college students learn how to ethically hack right into a simulated community to allow them to learn to shield it. It’s primarily for interns from schools and excessive faculties concerned in cybersecurity research.
The Changing into a Hacker course provides college students publicity to a real-world community (utilizing Cisco Modeling Labs [CML]). This simulated community acts extra like what they might see on-premises, utilizing bodily switches, routers, and firewalls. Cloud networks are sometimes extra locked down (rightly so) and behave otherwise. Changing into a Hacker additionally encompasses a simulated Wi-Fi community, so college students get uncovered to varied community sorts. We plan to have cloud targets within the Changing into a Hacker lab finally, so the scholars could have a mix of digital on-prem and in-cloud targets, getting the perfect of each worlds.
Changing into a Hacker has not too long ago turn into public, so anybody can entry the course supplies by way of Github. In fact, we don’t make the CML net interface public for safety causes, however we will shortly take it down and begin it again up at scale.
Whereas Changing into a Hacker is created by volunteers and isn’t an official Cisco product, it does present a terrific start line for patrons who need to create their very own hacker coaching eventualities utilizing a cloud account.
How a community hacking course can educate community safety
A course on moral hacking, often known as penetration testing or white-hat hacking, is essential for corporations in the long term, serving to them determine and repair vulnerabilities earlier than malicious hackers can exploit them, thus strengthening the community in opposition to future assaults. Coaching in moral hacking can even assist corporations adjust to safety rules and get monetary savings, avoiding the price of authorized charges, fines, and enterprise loss from information breaches. General, this type of coaching improves safety consciousness all through the group, main to higher safety insurance policies and coaching for workers to assist them acknowledge and reply to potential threats.
The premise is that while you engineer one thing to be safe, it’s essential to study to interrupt it. That method, you’ll know what to search for inside your individual networks. A standard discovering is an OS command injection vulnerability, an online vulnerability through which the attacker makes use of current APIs to execute arbitrary code by tacking on an extra working system command utilizing particular characters.
One instance is an online interface that permits you to ping a bunch so you may affirm reachability by means of that net interface, which can enable these characters to execute instructions aside from a ping. While you perceive the type of harm a hacker can do to your community, you may higher perceive the criticality of defending it.
Working with Cisco Modeling Labs for extra open coaching
These days, we’ve been working with the CML staff for Cisco’s inside coaching, which lets our moral hackers use CML to do safety testing for each Cisco product. Nevertheless, what began as a non-public mission is popping right into a probably vital alternative for an open-source answer.
It’s a wholly totally different method of constructing a community so as to do offensive safety testing. We’ve been operating it in Google Cloud, and it’s working nice.
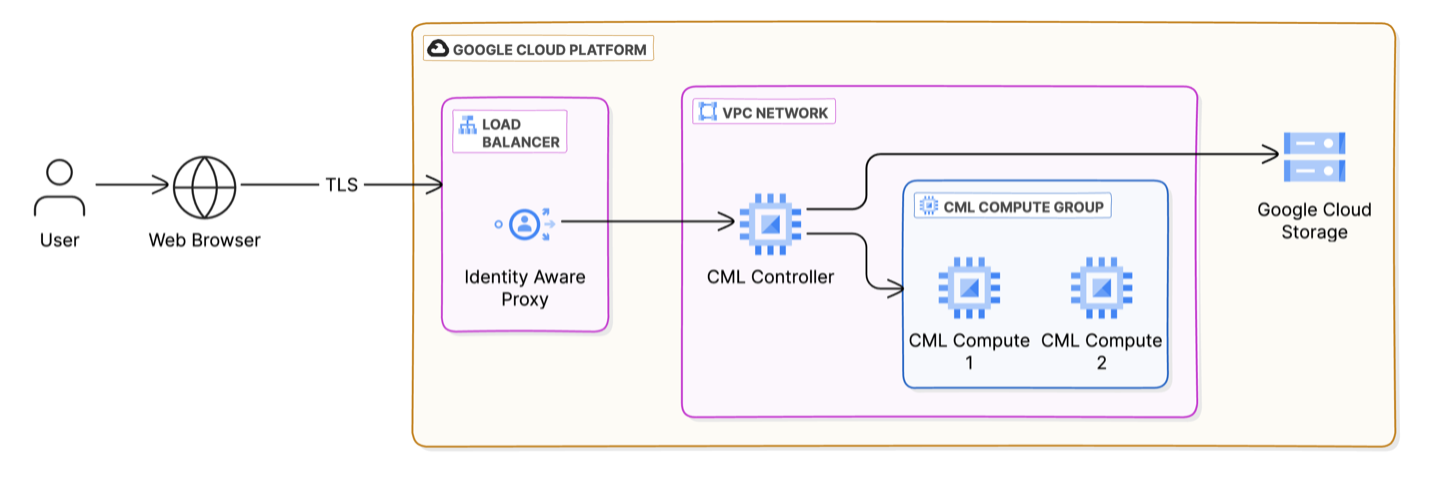
Cisco Modeling Labs deployment within the Google Cloud platform
We’ve been utilizing examples of Terraform configurations on DevNet. These configurations mean you can take the CML picture usually offered as an ISO picture or utility package deal and cloudify it for set up in Amazon Internet Providers (AWS) or Microsoft Azure. Terraform is a device for outlining and managing IT infrastructure utilizing code, or infrastructure as code (IaC). IaC makes it simpler to arrange, replace, and scale your sources constantly and effectively.
Whereas that was working properly, we quickly realized that to run it on the scale we would have liked, we must run CML on multiple bare-metal machine in a cluster in AWS—and that will get costly. We additionally required that every lab may settle for connections from the Web and provoke connections to the Web with IPv4 and IPv6 utilizing distinctive addresses. We discovered that the Google Cloud Platform met our wants properly.CML runs its personal hypervisor, which is software program that permits a single pc to run a number of digital machines (VMs) concurrently. The hypervisor is a safety measure.*
CML’s open-source hypervisor is predicated on Linux Kernel-based digital machine (KVM) and libvirt, a toolkit to handle virtualization platforms. It permits you to run digital machines on server {hardware} just like the Cisco Unified Computing System (UCS). This CML hypervisor can run nested on digital machine cases within the cloud and run digital machines by itself to help our labs.
Cisco Modeling Labs workbench interface
By taking this course with CML, customers connecting remotely with an online browser will get their very own pod (a bunch of digital, exploitable machines). And because it’s been working so properly for our inside groups, the CML staff was agreeable once I provided to write down the Terraform modules to make use of Google Cloud Platform to broaden our coaching.
I hope to doc a Google Cloud deployment and combine these modifications into the primary DevNet repository quickly.
Changing into a Hacker lab deployment
We need to make this methodology of provisioning labs for coaching extra common. The Changing into a Hacker Foundations course is the primary iteration of this methodology. We additionally supply different cybersecurity courses internally, however none use CML… but.
As a result of CML permits you to interface from wherever, you may entry your CML occasion on the cloud and do testing. It’s so compelling to make use of as a result of it’s all automated.
For instance, once we run a Terraform command, 20 pods (virtualized labs) are prepared to be used. We now have all of the configs to deploy it in case you have a CML subscription. Whereas not all the photographs are totally public as a result of it has a licensed Home windows picture, a person may simply create their very own photographs not offered out-of-the-box.
We hope to broaden this course over time. Keep tuned for more information on this nice alternative for Cisco coaching and CML that can assist you study extra hacking ideas and methods to higher safe your community.
NOTE: Cisco Modeling Labs is a business and formally supported product from Cisco. Be taught extra
Join Cisco U. | Be a part of the Cisco Studying Community.
Comply with Cisco Studying & Certifications
X | Threads | Fb | LinkedIn | Instagram | YouTube
Use #CiscoU and #CiscoCert to hitch the dialog.
*How we safe the Changing into a Hacker course
There’s no vulnerability in Cisco Modeling Labs (CML) that we all know of, however we’re deploying a lab (pod) that has gadgets in it which can be weak. CML permits you to make a networking topology, not just for routers but in addition for servers and hosts. You possibly can deploy a Linux or Home windows machine into it. It’s all primarily based on a kernel-based digital machine (KVM), a virtualization expertise that turns a Linux machine right into a hypervisor, permitting a number of remoted digital environments to run on a single host machine.
Hypervisors are vital to the safety of virtualized environments, particularly in the event you run machines which may execute weak code. Some vital methods hypervisors handle safety embrace:
Isolating digital machines (VMs) from one another ensures that if one VM is compromised, the attacker can not simply entry different VMs (which include recognized weak code) or the host system.
Controlling allocating {hardware} sources (CPU, reminiscence, storage, and community) to VMs to forestall useful resource exhaustion, the place one scholar lab can overload others.
Imposing strict entry management insurance policies so solely licensed customers and processes can work together with the VMs and the hypervisor itself, so college students solely see their digital machines and never others.
Implementing digital community safety measures, comparable to digital firewalls and community segmentation, to guard VMs from network-based assaults.
Sandboxing VMs to restrict their potential to work together with the host system and different VMs.
Listed below are a number of different safety measures we use for our Changing into a Hacker web site:
We isolate the location from the remainder of Cisco, which is one motive it’s vital to run CML within the cloud. If one thing had been to occur, we may shortly destroy the deployment and recreate it. Nevertheless, if this had been operating deep inside a Cisco lab, that will be harder and may hurt Cisco’s company community.
We shield the location with robust passwords generated throughout lab creation and multifactor authentication (comparable to Duo) utilizing the Id Conscious Proxy, which will also be turned on and off relying on the category’s viewers.
Whereas the lab has free entry to the Web, its pace is restricted; every pod can solely transmit a number of megabits per second.
We hold Area Identify Service (DNS) and move logs of individuals’s actions throughout the community.
Each pod has a singular IP handle, which we will hint to particular person college students.
Safe Organizations by Pondering Like a Hacker
Exploring AAA and TACACS Configuration with Cisco Modeling Labs
Share:
[ad_2]